Identity Services
Control how credentials are used across browser, desktop, SaaS, and privileged systems, without friction or breaking workflows.
Credentials are your weakest link
Every app starts with a login. SaaS, cloud consoles, collaboration tools, infrastructure systems. Identity is the gateway to everything. But once credentials are created, shared, or reused, control fades. Passwords live in unmanaged browsers. Privileged credentials are copied into local tools. Contractors log in from personal devices. Valid authentication becomes invisible activity.
Traditional identity tools verify who a user is. They do not control how identity is used after access is granted. That is where risk lives.
Control beyond the login
Island Identity Services are built directly into the Island Enterprise Platform, governing how credentials and privileged access are used at the exact moment work happens. Because Island operates inside the browser and across the endpoint, it binds credentials to user identity, device posture, and live session context. Password creation, autofill, sharing, and privileged access are all enforced by policy in real time.
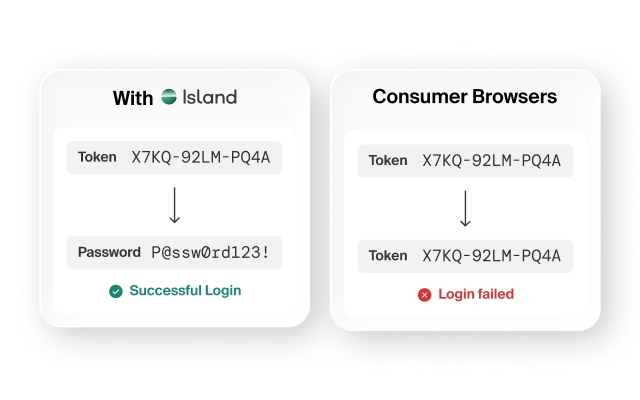
Privileged access to web applications, remote desktops, SSH, and SMB servers is mediated without exposing underlying credentials. Users never directly possess high-risk passwords. For applications that do not support federated login, Protected Accounts extend your single sign-on framework, ensuring those tools operate inside the same governed identity model as the rest of your environment.
The result is identity that does not stop at authentication. It governs the session through the entire workspace.
Every app starts with a login. SaaS, cloud consoles, collaboration tools, infrastructure systems. Identity is the gateway to everything. But once credentials are created, shared, or reused, control fades. Passwords live in unmanaged browsers. Privileged credentials are copied into local tools. Contractors log in from personal devices. Valid authentication becomes invisible activity.
Traditional identity tools verify who a user is. They do not control how identity is used after access is granted. That is where risk lives.
Island Identity Services are built directly into the Island Enterprise Platform, governing how credentials and privileged access are used at the exact moment work happens. Because Island operates inside the browser and across the endpoint, it binds credentials to user identity, device posture, and live session context. Password creation, autofill, sharing, and privileged access are all enforced by policy in real time.
Privileged access to web applications, remote desktops, SSH, and SMB servers is mediated without exposing underlying credentials. Users never directly possess high-risk passwords. For applications that do not support federated login, Protected Accounts extend your single sign-on framework, ensuring those tools operate inside the same governed identity model as the rest of your environment.
The result is identity that does not stop at authentication. It governs the session through the entire workspace.
Unify credential control

Govern credential creation, storage, sharing, and privileged access with one platform through a single policy engine integrated with your IdP.
Contain credential risk

Bind passwords & privileged sessions to identity, device posture, and live context. Control reuse in unmanaged devices or off-platform sessions.
Frictionless access

Autofill credentials, mediate privileged sessions, and extend SSO to non-SSO apps directly inside the browser that employees already use.
Capabilities
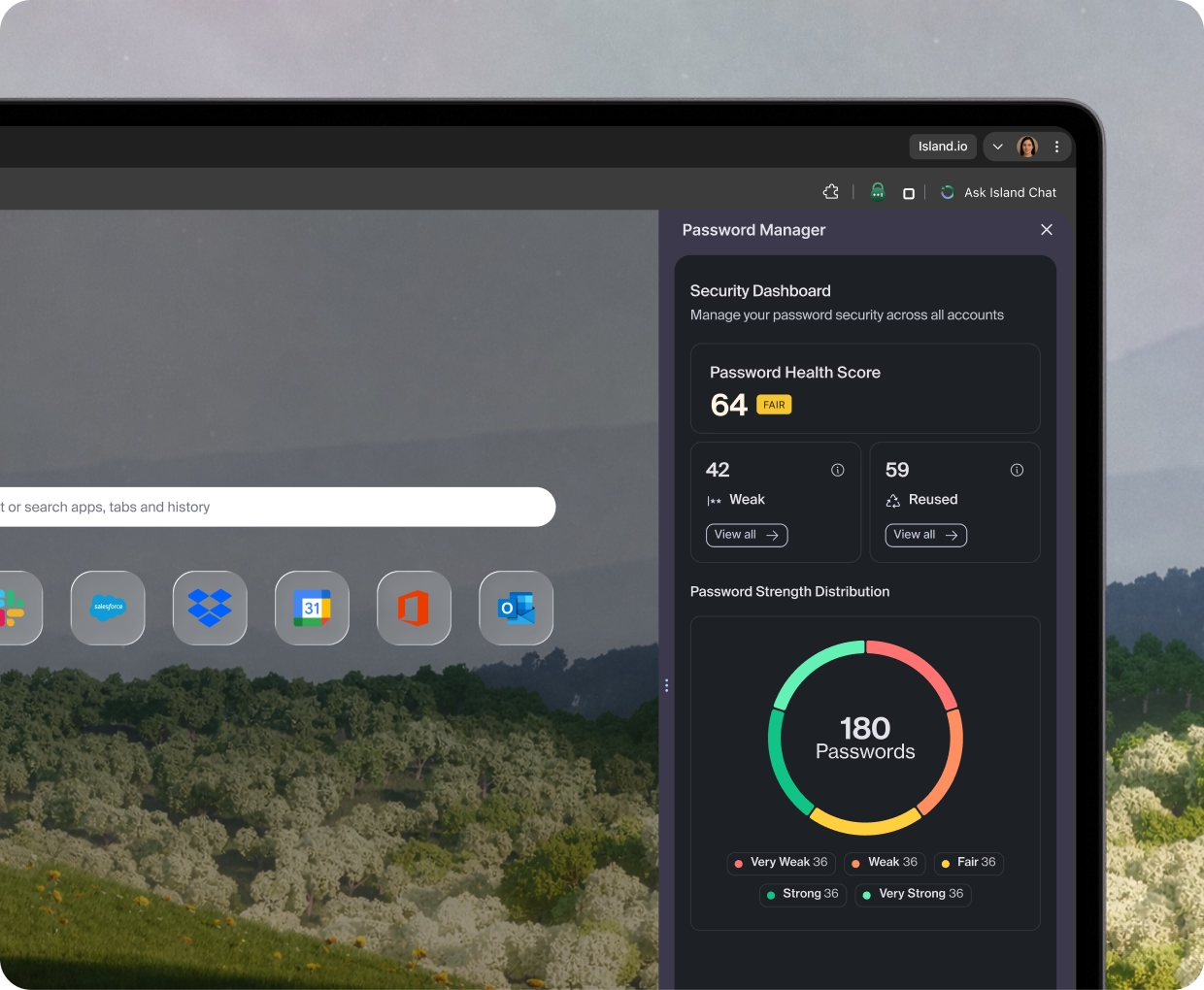
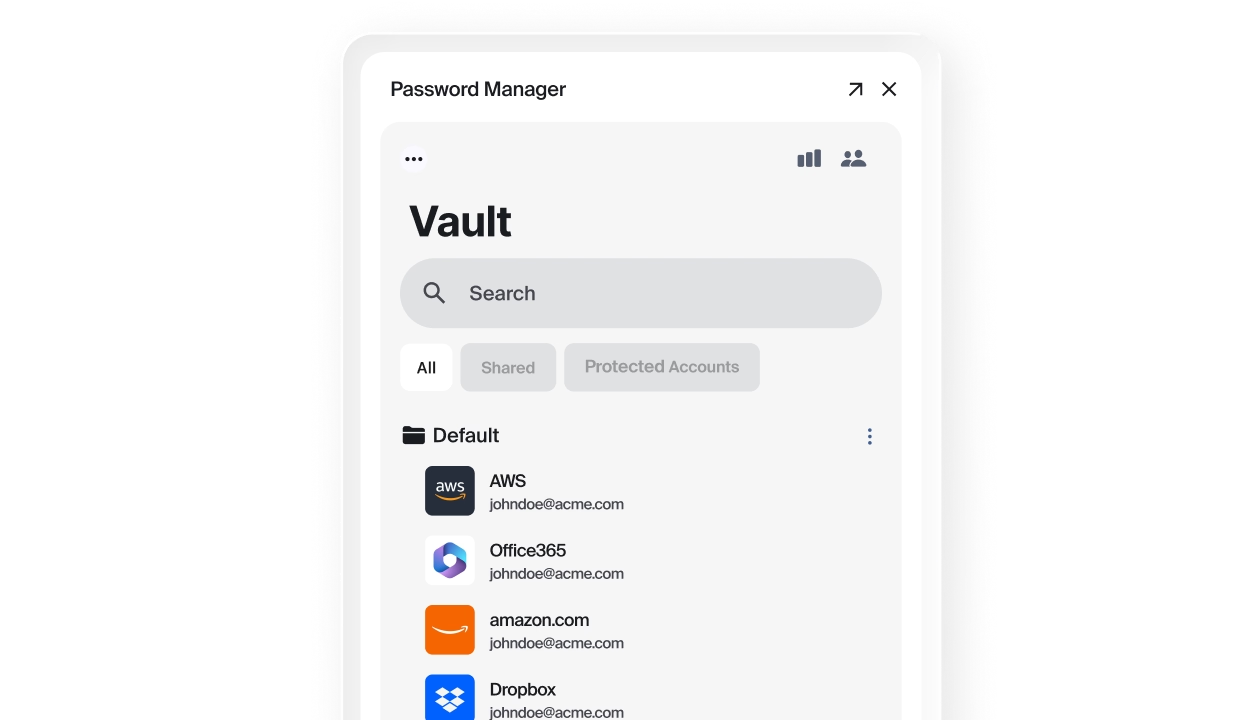
Island Enterprise Password Manager
Secure passwords right where they’re actually used. Island gives you global, enterprise-grade password governance across browser, desktop, and mobile, without changing how people work.
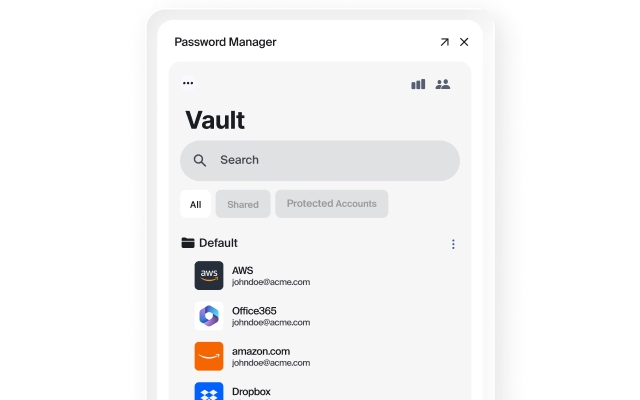
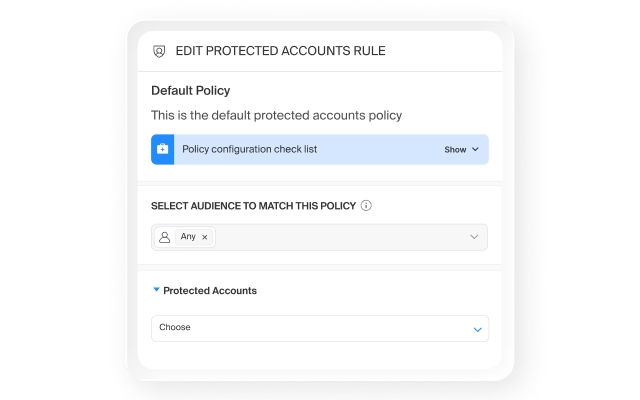
Island Protected Accounts
Extend single sign-on to non-SSO applications by intercepting credentials and binding them to identity, posture, and session context, so every app operates within the same access framework, regardless of whether it was built for it.
Privileged Access Management
Ensure users never directly possess credentials for shared or high-risk systems by facilitating access via Island without revealing plaintext passwords.
Why identity services matter
FAQ
Finance: Secure access to trading/CRM apps with no‑download or copy/paste, meeting compliance while enabling remote work.
Healthcare: Apply DLP controls to EHR systems for HIPAA compliance, keeping patient data safe on personal devices.
Retail: Give vendors access only to specific apps with identity checks and restricted data actions, reducing supply chain risk.
Technology: Protect source code and customer data on BYOD by enforcing policies in the browser without managing the whole device.
Business Process Outsourcers (BPOs): Provide secure, monitored application access and workflow automations to agents, whether you are a BPO or an organization that relies on BPOs.
Government: Consolidate technology for reduced spend, comply with policies and directives, protect and monitor data, mitigate insider threats, and much more.
Higher Education: Ensure compliance and modernize security with an exceptional user experience for all, from students to staff.
And many more, including hospitality, manufacturing, law, and pharma.
No. Island Identity Services is built to work alongside your existing identity provider, not replace it. Okta, Azure AD, Ping, or whatever IdP you rely on for authentication and SSO continues to do that job. Island handles everything that happens after authentication: how credentials are used, shared, and reused across browser, desktop, SaaS, and privileged systems, in real time, bound to device posture and session context. If your IAM strategy has a gap between "who is this user?" and "what are they actually doing with their access?" that is precisely where Island operates.
Yes. Identity doesn't end at authentication. Island’s continuous, context-aware identity controls follows users across every app, device, and workflow by governing credentials and access inside the browser, across the endpoint, and in real time. Rather than bolting identity controls onto the perimeter, Island binds credentials to user identity, device posture, and live session context, enforcing policy continuously throughout the session rather than just at the front door.
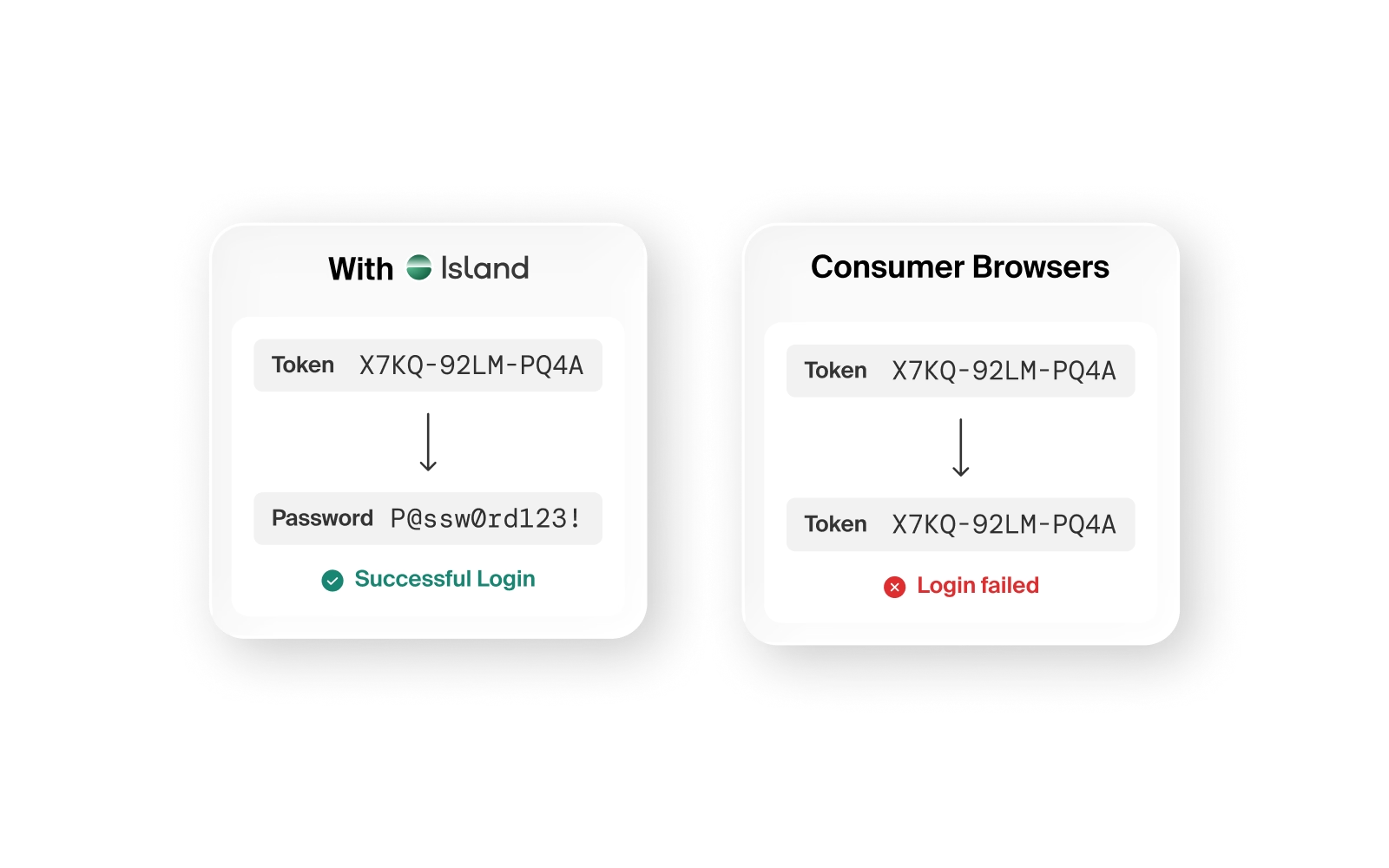
Yes. Most enterprise environments include at least a handful of applications like legacy tools, older SaaS platforms, or built-in-house business applications that were never designed to support modern federated identity standards. These apps typically fall outside your SSO framework entirely, meaning employees create and manage separate passwords that live outside any governed system. Island Protected Accounts solves this by intercepting credentials for these applications, replacing them with a secure token not known to the user. This ensures these accounts are only accessible via Island, binding them to the same identity, device posture, and session context that governs everything else in your environment. The result is that every application, regardless of how it was built, operates inside the same access framework.
Yes. Island is built around the “never trust, always verify” core principles of zero trust, but extends them further than most zero trust architectures reach. Traditional zero trust frameworks verify identity and device posture at the moment of login, then grant access based on those signals. Island implements zero trust as a continuous enforcement model, not a one-time check, continuously evaluating identity, device posture, location, and session context throughout the entire session. If something changes mid-session (a device becomes compromised, a user attempts to move data outside approved boundaries, or a privileged credential is misused) Island can detect and respond in real time.
Eliminate the threat of single-actor changes by adding an external approval workflow and strengthen your authentication flow with an MFA challenge attached to any action or workflow. Island can insert approval steps and MFA challenges into any web application workflow immediately, without requiring API access, vendor cooperation, or application modifications. This means you can add governance to legacy systems, SaaS applications, or any web-based admin console within hours, not months.


.svg)
.svg)
