Endpoint Services
Protect, monitor, and support user devices and workstations.
.avif)
Endpoint management is complex
Protecting managed and unmanaged devices is both critical and difficult to do well. Devices are frequent attack vectors for compromising company data and resources. But administrators often have limited visibility into these devices, especially if they are unmanaged BYOD or third-party contractor devices.
Island makes it easy
Island gives you a comprehensive solution to protect, monitor, and support your end users’ devices. This includes automatically detecting and mitigating suspicious device activity, such as browser tampering, interception attempts, debuggers, memory inspection, or risky software. Island also provides real-time visibility into device state, allowing administrators to assess devices, hunt threat activity, and perform forensic investigations. Lastly, IT staff can remotely access devices (with end-user notification and permission) to provide technology support and assistance.
Protecting managed and unmanaged devices is both critical and difficult to do well. Devices are frequent attack vectors for compromising company data and resources. But administrators often have limited visibility into these devices, especially if they are unmanaged BYOD or third-party contractor devices.
Island gives you a comprehensive solution to protect, monitor, and support your end users’ devices. This includes automatically detecting and mitigating suspicious device activity, such as browser tampering, interception attempts, debuggers, memory inspection, or risky software. Island also provides real-time visibility into device state, allowing administrators to assess devices, hunt threat activity, and perform forensic investigations. Lastly, IT staff can remotely access devices (with end-user notification and permission) to provide technology support and assistance.
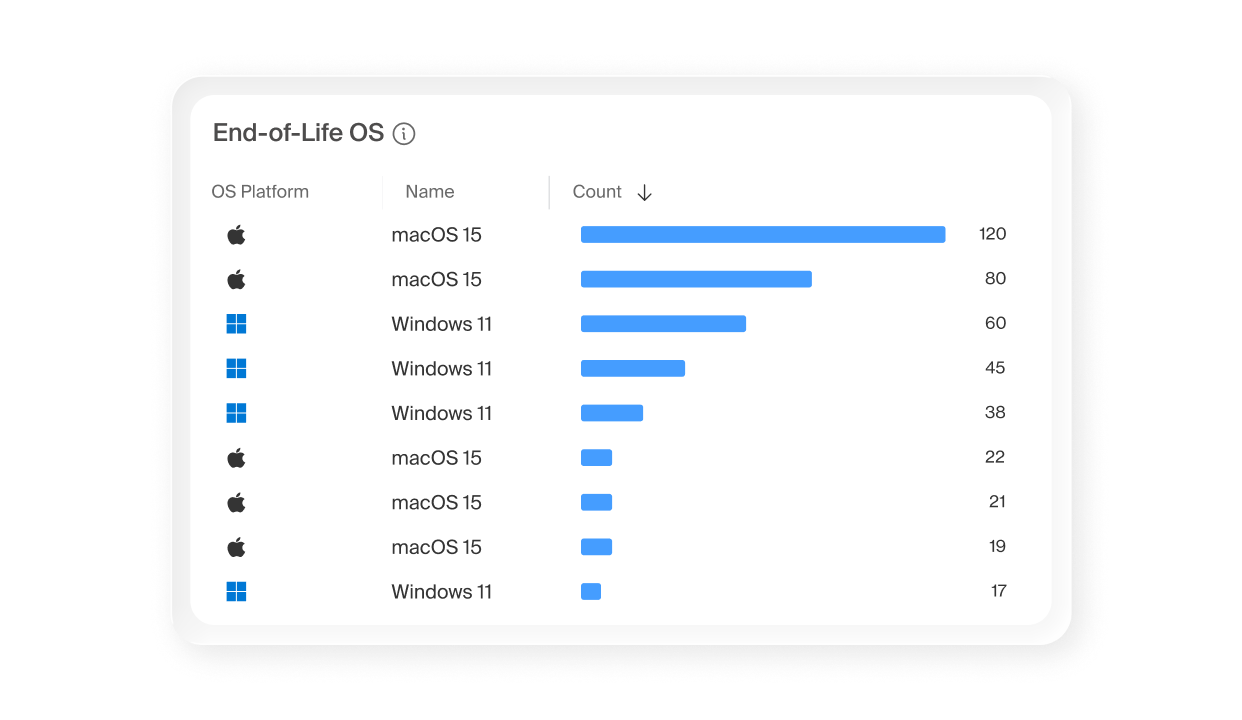
Get immediate visibility

Get real-time endpoint visibility to answer critical questions about devices, software, and configurations as issues happen, not hours later.
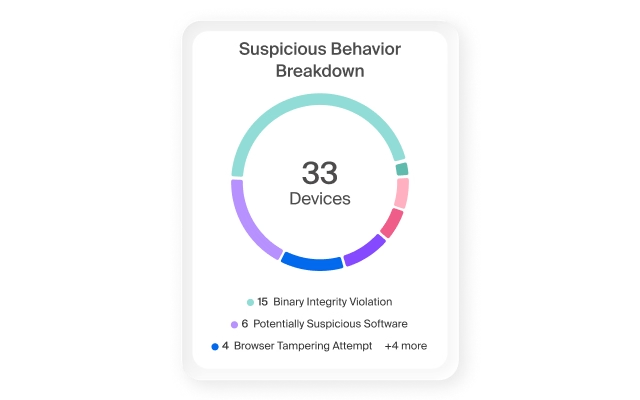
Automatically protect

Detect and mitigate suspicious activity on the device according to policy, preventing threat actors from continuing accessing applications.
Provide support

Enable IT support to remotely access user devices with their permission to troubleshoot technology problems.
Capabilities
Device Control
Island Device Control provides secure, policy-governed remote access for IT support with full user transparency and session logging.
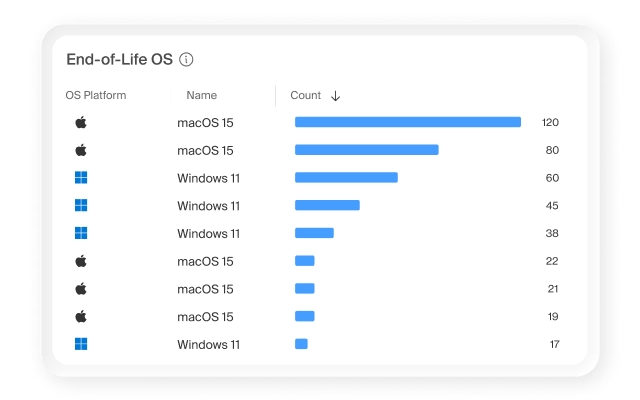
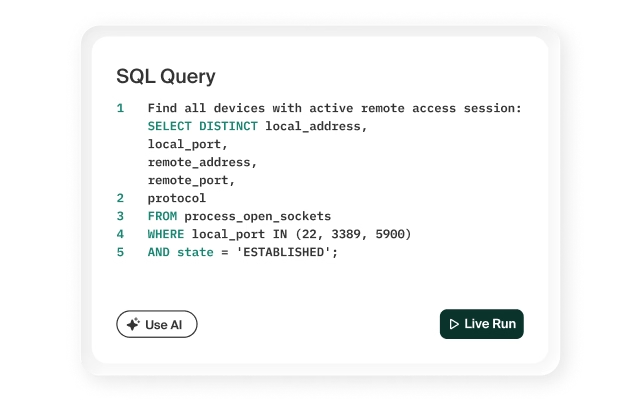
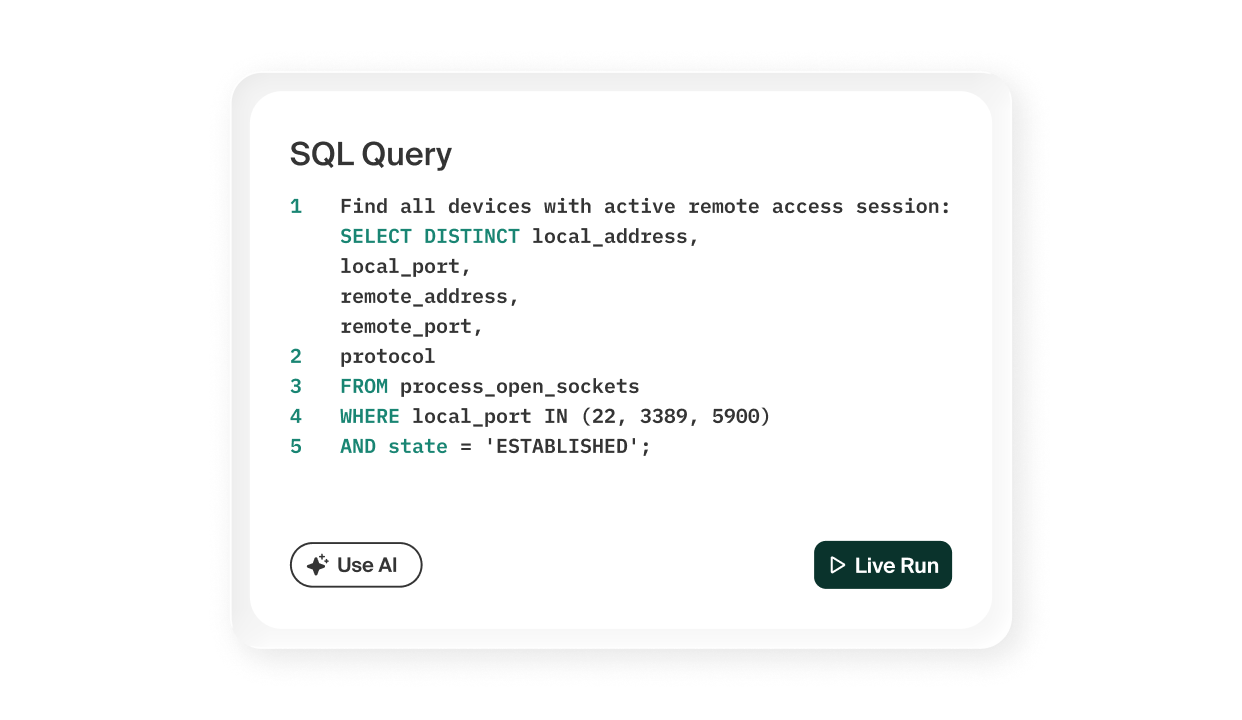
Device Query
Island Device Query enables IT teams to inspect device state in real time, including running processes, installed applications, and system configurations.
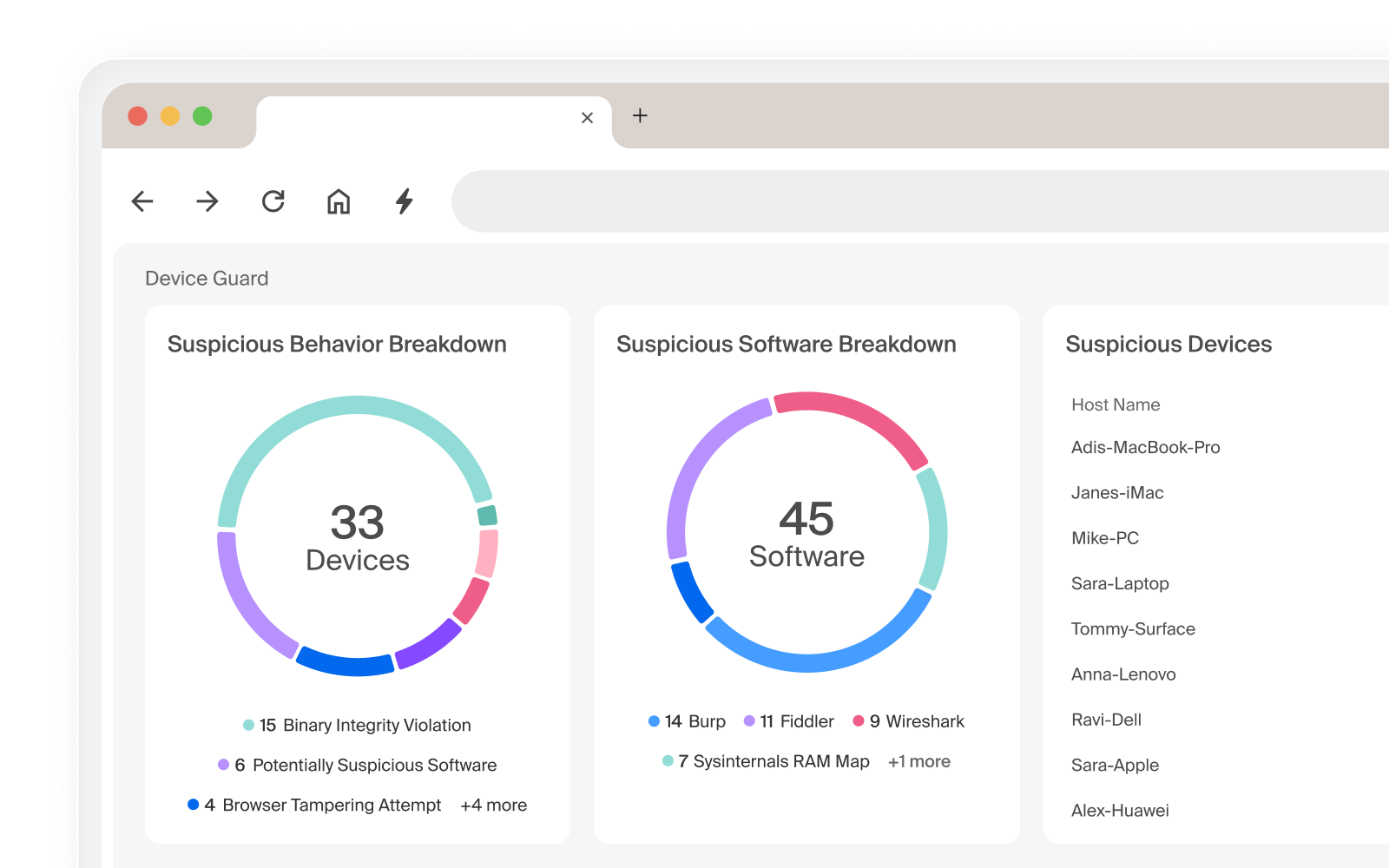
Device Guard
Island Device Guard detects suspicious activity then adjusts access based on configurable security policies.
Why endpoint services matter
FAQ
Yes. Three capabilities work together to monitor and protect all your company’s devices, whether managed devices or BYOD items like phones and tablets. Island’s Device Guard automatically detects suspicious activity — including browser tampering, interception attempts, debuggers, memory inspection, and risky software — and adjusts application access privileges according to policy before a threat can progress. Device Query gives IT and security teams real-time visibility into device state, including running processes, installed applications, and system configurations, supporting threat hunting and forensic investigations as incidents unfold. Device Control enables IT staff to remotely access user devices for support, with end-user notification and full session logging built in. All three capabilities run through the same policy console that governs the rest of the Island platform.
Yes. While Island can fully replace traditional endpoint security tools, Island's endpoint capabilities also work with in-place complement existing EDR and other solutions. Where traditional endpoint security focuses on detecting and responding to threats at the OS and file system level, Island adds a layer that existing tools can't see: what's happening inside the browser and at the point where users actually access applications and data. Device Guard, Device Query, and Device Control extend that coverage to device-level activity without duplicating what your EDR already does well. The result is a more complete picture of endpoint risk, with context that flows directly into access policy across the entire Island platform.
No. VDI handles device access by streaming a remote desktop, adding infrastructure complexity and a degraded user experience to solve what is ultimately a security and control challenge. The Island Enterprise Platform starts where users actually work and weaves security, access, identity, data protection, and productivity directly into that experience. Users log in and work naturally across web applications, thick desktop apps, internal resources, and AI tools, all governed by real-time context like role, device posture, and location. It’s all the capabilities and benefits of desktop virtualization solutions, but without VDI’s complexity, expense, and performance issues.
Yes. Through Device Query, Island gives IT and security teams real-time visibility into device state (including running processes, installed applications, and system configurations) across any device where Island is installed. This is particularly valuable for BYOD and contractor devices, where traditional endpoint agents either can't be deployed or create friction with users who don't want corporate software on personal hardware. Island operates through the browser and Island Desktop, a background service that is installed optionally alongside the browser, to extend visibility to devices that would otherwise be blind spots. When an incident occurs, security teams get answers in real time instead of waiting hours for telemetry to catch up.
Yes. Consolidation is one of the most compelling reasons organizations move to Island. The traditional enterprise security stack grew by accumulation: a VPN for private access, a CASB for cloud visibility, a DLP solution for data protection, a PAM tool for privileged credentials, an endpoint agent for device security, and separate tools for AI governance and productivity. Island folds all of these capabilities into a single platform governed by one policy console, built around the place where your users already do their work: the browser.

.svg)
.svg)
